Upgrade Entities to CVE-recalled Releases
By default, Apollo will not upgrade an Entity to a recalled Release. This is desired in most cases but can also contribute to a deteriorated security posture. When an Entity's current Release is CVE-recalled, refusing to upgrade to a less vulnerable CVE-recalled Release prevents Apollo from improving the Entity's security posture and can prevent step-through upgrades to the latest Release.
When enabled, Apollo can propose an upgrade from a CVE-recalled Release to another CVE-recalled Release as long as the upgrade improves the Entity's security posture. Apollo continues to prefer non-recalled Releases when one is available, meaning that CVE-recalled Releases are only considered when there is no eligible non-recalled target.
Enable upgrades to CVE-recalled Releases
To enable this feature, navigate to the General tab of the Hub Settings page from the main Apollo sidebar and set Enable Upgrades to Releases Recalled for Vulnerabilities to True.
This Hub-level setting can be overridden for a specific Environment from that Environment's Settings tab under Settings overrides. The override takes precedence over the Hub-level value, which lets you opt individual Environments in or out independently.
Eligibility
For Apollo to propose an upgrade to a CVE-recalled target Release, all the following must be true:
- The target Release is affected only by security vulnerability recalls. Releases with any user-created or other non-CVE recalls remain ineligible. The current Release can be affected by non-CVE recalls.
- The current and target Releases each have a vulnerability scan completed within your Hub's re-scan SLA. Stale or missing scans block the upgrade until a fresh scan is available. Apollo will trigger re-scans automatically when doing so could unblock an upgrade.
- The target Release's risk score is less than or equal to the current Release's risk score.
- The target Release has no ClamAV (malware) findings. The current Release may have ClamAV findings, but Apollo will never advance an Entity to a Release with malware findings.
If no target satisfies these requirements, Apollo surfaces a constraint with information on why the upgrade is not possible.
Risk score
Each Release has a risk score on a bounded 0–10 scale, where 0 means no active vulnerabilities and 10 is the maximum. The score is computed from the CVSS scores of the active (out-of-grace, unsuppressed) CVEs detected by the latest scan and reflects both:
- The severity of the worst vulnerability in the Release, taken as the highest CVSS score among its active CVEs, so a single critical CVE is never masked by an otherwise quiet Release; and
- The cumulative volume of vulnerabilities, aggregated across the CVSS scores of every active CVE, so the gradual accumulation of lower-severity findings is captured.
CVEs without a published CVSS score are assigned a representative value based on the scanner-reported severity tier so that every active CVE contributes to the score.
The exact formula and its tuning constants are managed by Palantir and are not configurable.
Inspect risk scores on a Plan
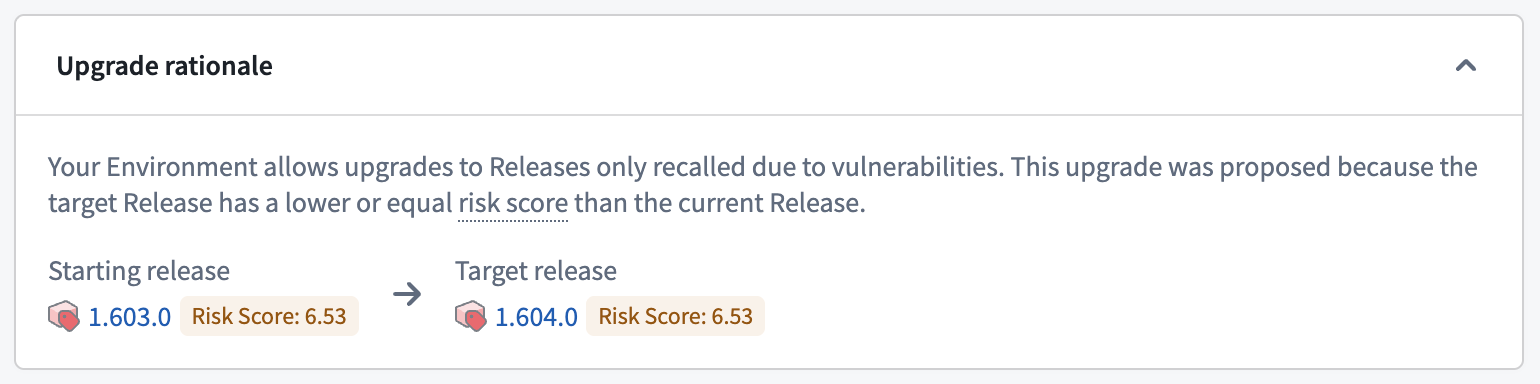
When a Plan is proposed via this workflow, Apollo records both the current and target Release risk scores as metadata on the Plan. You can review these values when inspecting the Plan to confirm why a CVE-recalled target was selected and to verify that the upgrade reduces (or maintains) the Entity's risk score. Plans whose target was not selected via this workflow do not carry risk score metadata.